Authentik OAuth/ OIDC Setup - Portainer
Authentik uses many ways to connect to services, one being OAuth or Open ID Connect. This method is widely used on many services, such as Portainer.
Please follow Authentik and Portainer documentation
Authentik OAuth:
- Login to Authentik Admin Interface
- Go to Applications and select Create with Provider
- Choose a name and group
- Under URI in Launch URL enter https://portainer.cyberpaw.org
- Choose Oauth2 Provider
- Name the provider same as application
- For Authorization Flow choose Cyberpaw-authorization-flow (or default one)
- Make sure Confidential is selected for Client Type
- Copy Client ID and Client Key
- In Redirect URIs enter https://portainer.cyberpaw.org (check portainer instructions for more detail)
- For Encryption key choose default-authentic-self-signed-certificate
- Under Advanced flow settings choose Welcome to Authentick (or default one)
- Under Configure Bindings click Bind existing policy/group/users
- Select Group and choose existing group that is authorized to use this service
- Review and Submit
- The provider is created and should say it's connected to application
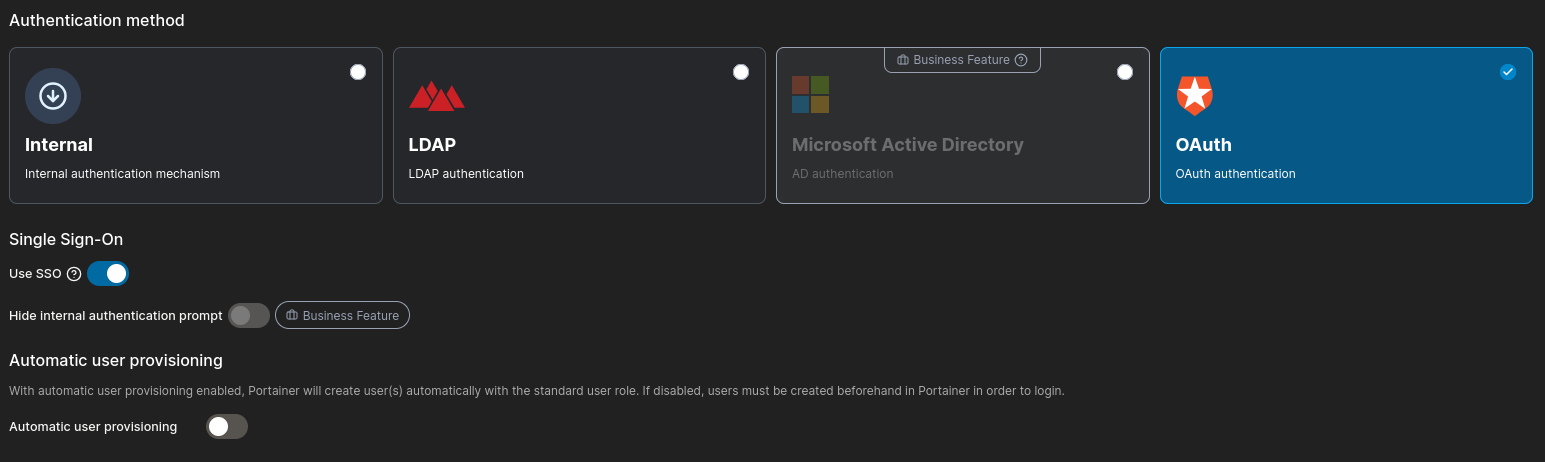
Portainer Steps:
- Choose Automatic User Provisioning allowing other Authentik users that don't have Portainer user can login
- If not selected you will need to create an account with same email as Authentik user
- Scroll down to OAuth Configuration
- Copy and Paste all the field ID, secret and URLs from Provider information in Authentik
- Go back to Authentik Admin Interface
- Lower Application Section and click Providers
- Click on Portainer Provider and copy all the required information to Portainers OAuth Configuration
- For User Identification type "email"
- For Scope type "email oauth provider" -Portainer documentation says to use dashes but use space instead
- Save
- Copy and Paste all the field ID, secret and URLs from Provider information in Authentik
- Logout and you should see Login with OAuth button